More people working from home has led to increased cyber attacks on businesses across Japan. Here are a few WFH Do’s and Don’ts to help prevent cyber attacks, making your home office a safer one.
Since the COVID-19 pandemic emerged just over a year ago, many facets of our life have been disrupted. Job-life included. As society scrambled to adapt and protect itself from this mysterious virus, buzzwords like “new normal”, “social distancing”, and “working from home” (aka WFH) entered our vernacular and have now become commonplace.
Despite the numerous positive results working from home has yielded employees and businesses — such as improved productivity, less commute stress, and saving money — the hasty shift has also created a list of cybersecurity issues. Put simply, we’re more vulnerable than before and the window of opportunity is wider than ever for cyber criminals to strike.
Japanese Companies Targeted
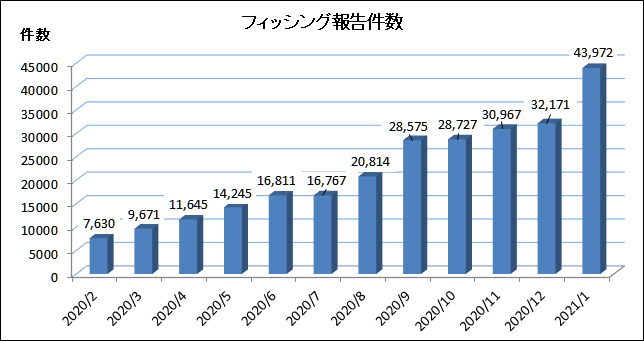
While last year brought several attacks on big names from abroad like Zoom, Twitter, SolarWinds, and Marriott, Japan also suffered a cyber thrashing of sorts.
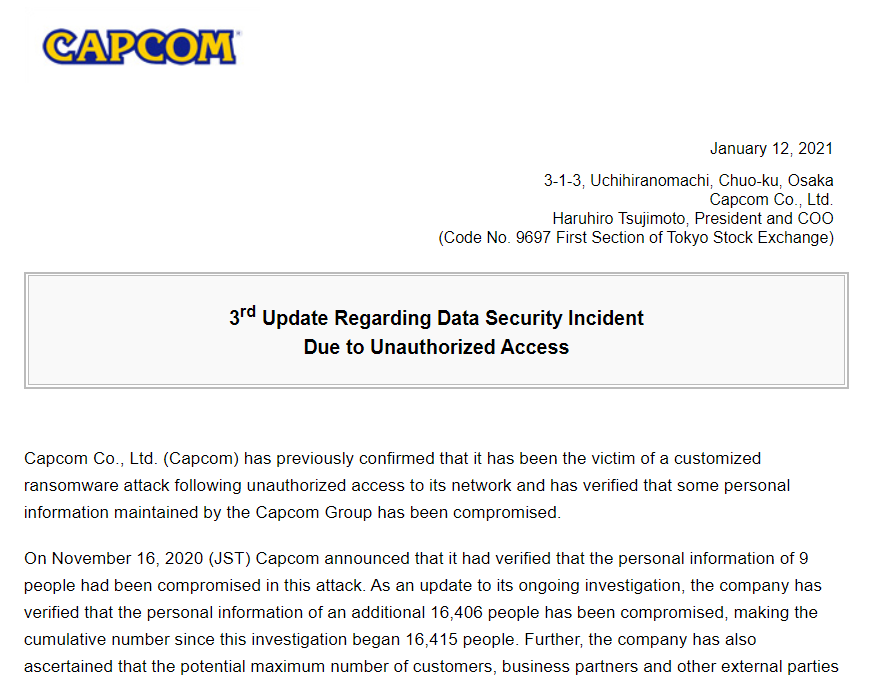
Take the following cases, both of which happened within the past 3 months of this writing. First, in November 2020, legendary Japanese game company Capcom made headlines after it fell victim to a ransomware attack by Russian hacker group Ragnar Locker. Although Capcom refused to cave under the 1.1 billion yen demand, they have since confirmed that the attack resulted in the theft of over 16,400 people’s personal information — though its estimated upwards of 390,000 people may have been affected. And in the second case, PayPay Corp., a smartphone payment service provider, had one of their servers unlawfully accessed in December. It’s reported that 20.7 million items of information may have been compromised.
But wait, there’s more…
Tokyo Shoko Research Ltd. released a survey that paints a grim picture of how much damage cyber attacks caused Japan in 2020. According to the survey, 88 publicly traded companies and their subsidiaries experienced a compromise or loss of personal information. A total of 25.15 million people were affected! And here’s the kicker… that number may pale in comparison when accounting for Japan’s unlisted firms. Experts have cited the failure of companies to take proper security measures while rushing the promotion of WFH as contributing factors to the surge in attacks.
Prevent Cyber Attacks – 5 Remote Work DO’s and DON’TS
So what can you do to greatly decrease the chance or even prevent cyber attacks while working remotely in Japan? Here are 5 useful WFH DO’s and DON’Ts.
1. DON’T Use unsecured networks such as public Wi-Fi.

It may be convenient, but you sacrifice security for that convenience. Using public Wi-Fi leaves you exposed to potential threats like:
Infection: You may catch malware from an infected device on the public network.
Rogue networks: Hackers can create fake networks with names that appear to be legitimate, thus baiting incautious users to hop on. The hacker will then eavesdrop on communications between the user and the websites they visit, hoping to intercept sensitive information like passwords and credit card numbers.
Shoulder surfing: You never know who might be watching. An attack doesn’t need to be high-tech in order to be effective!
2. DO Use a Virtual Private Network (VPN) for extra security.

VPNs are a great solution to prevent cyber attacks because they protect the data you send over the net by encrypting it. Even if, by chance, someone were to intercept your communications, the data would be indecipherable. In addition, a VPN provides security by hiding your personal IP address and physical location.
Personal versus Enterprise VPNs
There’s two types of VPNs you should know about: personal and enterprise (the latter sometimes referred to as business or corporate). Let’s take a quick look at the differences each one provides the user.
Personal VPN: Setting up this type of VPN is usually as simple as downloading the required software from the service provider’s website, logging onto your account, then connecting to the virtual private network of your choice. Therefore, you control the account and devices that connect to the network. As for maintenance, the service provider is in charge of keeping things running smoothly. As the name implies, personal VPNs are geared towards keeping you protected and anonymous while accessing the web.
Enterprise VPN: Setting up and maintaining this kind of virtual private network requires technical expertise. Scope of protection is limited to the corporate network. The company can still monitor your traffic, the sites you visit, and the devices connected. When you hop onto an company VPN, you have access to the same private resources you normally would as if you were physically there which is quite convenient.
*If your employer hasn’t provided you with access to a company VPN, reach out to us here and we will share a list of our favorite personal and enterprise level VPN solutions and reasons why.
3. DO Use Multi-Factor Authentication (MFA) to access accounts and services.
If you want to prevent cyber attacks, the traditional single-factor authentication is not recommended because a hacker only needs one piece of information to successfully attack you. Using MFA ensures that at least one extra step is in place to verify your identity. For example, the bank sends a time-sensitive pass code to your smartphone whenever you attempt to log in. A hacker would need to have stolen your device to know this code, something which is less likely to happen. In general, options to use MFA can be found inside your account Settings or Security areas.
4. DON’T Click on links or open attachments inside suspicious emails.

Watch out for emails that appear to be from companies or sources you trust. These emails will often carry a subject line and message of urgency — the goal being to have you take immediate action by clicking on the enclosed link or attached file. Don’t do it; this may be a Phishing scam! If the email in question is from a company where you hold an account or someone you know, we recommend contacting them directly with info you know is real such as their telephone number or official website.
To report phishing emails, please use the following help pages:
Council of Anti-Phishing Japan (Japanese only)
Federal Trade Commission – Report Fraud
5. DO Use strong passwords and a password manager.

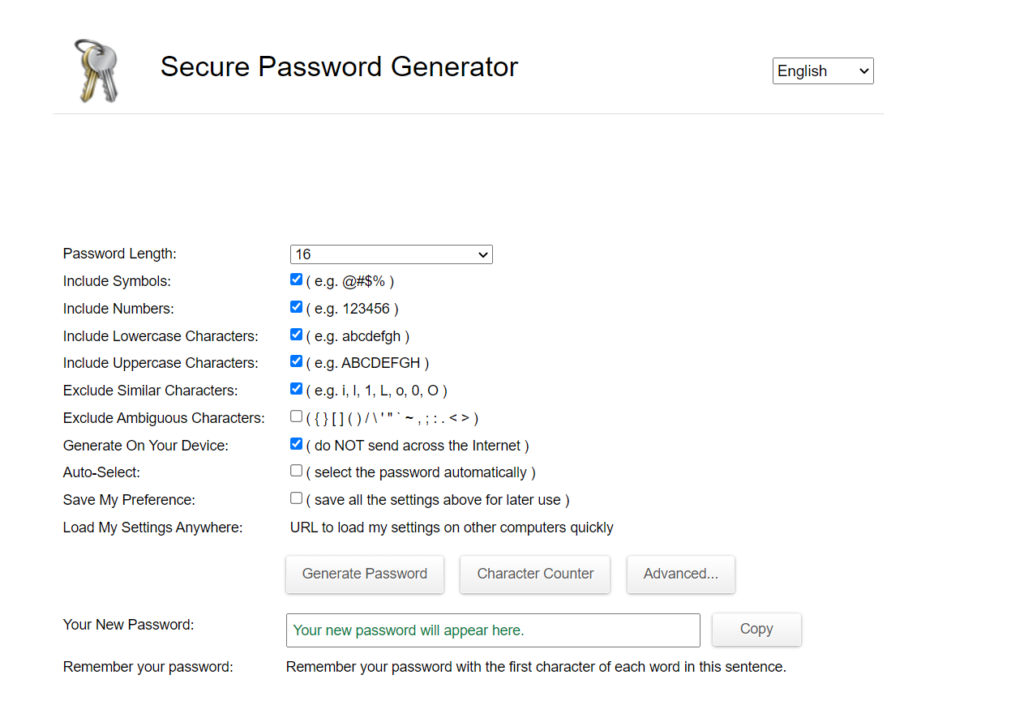
Be sure to use passwords that have a mix of numbers, upper and lowercase letters, and symbols. Never include personal information as part of your passwords! And don’t use the same password for different accounts. To generate passwords that meet this criteria, I recommend checking out the following two tools…
The first tool is EXPERTE’s Password Generator, a free, lean, and powerful generator. EXPERTE has the customization options we look for, such as the ability to add further complexity to your password with numbers, symbols, and so on. It also allows you to adjust the length of the password, letting you choose from a minimum of 4 characters all the way up to a whopping 50!
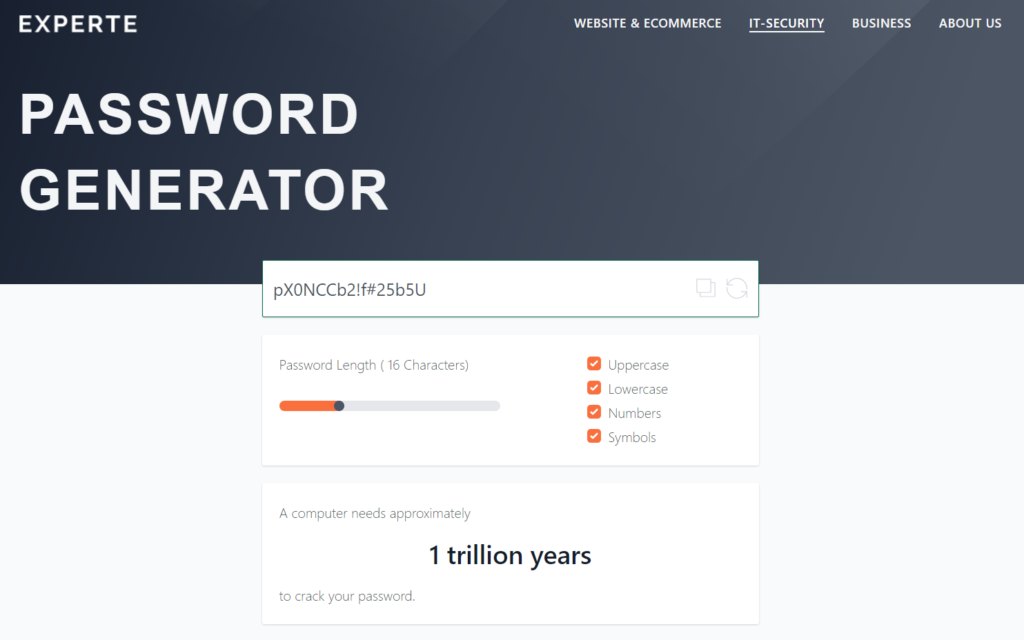
In addition to creating strong passwords, EXPERTE’s password generator will also check if a password you provide it has been leaked or has been part of a data breach. Information like that can be extremely helpful, especially for on-the-spot secure password decision making. The tool can estimate how long a password would take to uncover in a brute force attack. (FYI: as an extreme example, a password of 50 characters in length would take *drumroll* 16 quattuorvigintillion years to hack.) EXPERTE’s tool is, as of this writing, also available in German, Italian, and French with the possibility of expanding to other languages in the future.
The second generator we recommend the tried-and-true Strong Random Password Generator — which is also free — and can be found here!
Next, you’ll benefit from having a place that keeps all your strong passwords safe, organized, encrypted and in one place. A password manager does just that. And to top it off, you’ll only need to remember one password — a master password — to access your manager.
*Not sure which Password Manager to use? Reach out to us here and we’ll help you find the right one.
Getting Through it Together, Emerging Stronger

The global effort to quickly transplant a large portion of its workforce in the face of a pandemic has been no small feat. Nearly a year later, the benefits and drawbacks of working from home have become clearer. With many signs indicating that telework is here to stay (for now), the responsibility falls on companies to have comprehensive and effective cyber security policies in place, and to thoroughly educate their employees.
On the other hand, more employees need to follow the WFH best practices as defined by their companies. And it will be through a consistent effort from both sides that the window of opportunity — which threat actors have been taking advantage of — shall begin to shut.
Need Help Boosting the Security
of Your WFH Office?
Image credits: katemangostar, stories, Council of Anti-Phishing report 2021/01